Switch Project Management Platforms
Without Losing a Single Day of Work
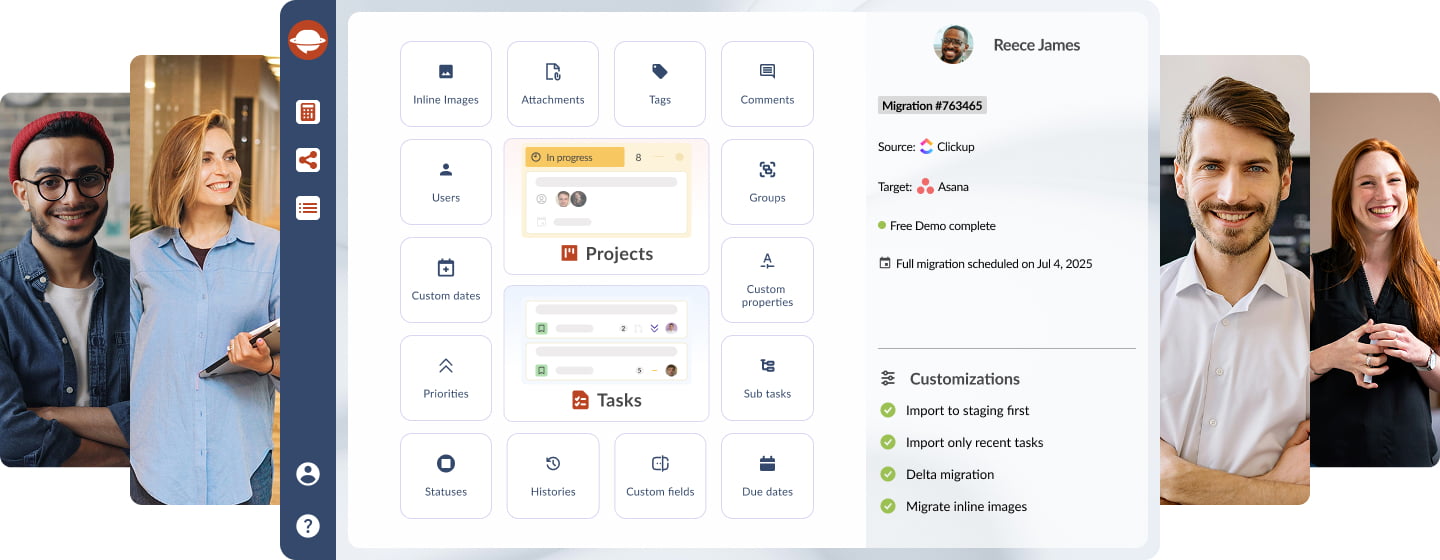
The Secure, Automated Infrastructure to Migrate 50+ Project Management Tools
Changing your tech stack shouldn't stall your momentum. Project Management Migration Service provides a high-precision bridge, ensuring immediate operational readiness. Join 20,000+ companies who have moved millions of records with 1:1 data parity.
See your data in the new system in minutes

The Project Management Migration Service Guarantee
Validate Before You Commit: Run a Free Demo Migration with your live data samples.
Retain Total Context: Every task, subtask, attachment, and @mention stays linked, so your project context remains intact.
Custom Logic: Filter by date, status, or project type to ensure only high-value data enters your new project management system.
Business Continuity: No need to "pause" your projects. Your team stays productive while our Migration Wizard handles the transfer. Switch platforms when you are ready, not when the data is ready.
Enterprise-Grade Security: Your data is encrypted and protected at every step.
No credit card required Trusted by 20,000+ teams Zero downtime guaranteed

Infrastructure & Data Security Standards
Project Management Migration service is built on SOC-compliant AWS infrastructure. We implement multi-layer protection to ensure data remains isolated and encrypted throughout the entire transfer lifecycle.
Encryption Protocols: We use industry-standard encryption for both data-at-rest and data-in-transit (TLS 1.2+), including secure session management.
Identity & Access Management (IAM): Secure your migration environment with Multi-Factor Authentication (2FA) and Role-Based Access Controls (RBAC).
Regulatory Compliance: Technical workflows are aligned with GDPR and HIPAA requirements for data handling and privacy.
Superb service, very secure and great attention to detail
"I was especially concerned about security. Relokia described their approach and I was impressed with how well-thought-out their process was and how respectful they were of customer data."
Brett Jackson
VP of Operations at PillDrill

Managed Migration & Structural Integrity
Our managed workflow eliminates manual scripting, enabling complex transfers without internal developer resources.
Precision Schema Mapping: Map standard/custom fields, tags, and user associations to ensure 1:1 data parity.
API-Driven Context Preservation: Maintain "connective tissue," including original timestamps and task nesting, to protect long-term reporting accuracy.
Audit Trail Preservation: Migrate comments, @mentions, and original timestamps. All historical data remains searchable and valid for compliance auditing.
Relational Mapping: Automated preservation of task-to-subtask hierarchies, dependencies, and original user ownership. We eliminate the need for manual record re-linking.
"The mapping was incredibly precise. We moved thousands of records and didn't lose a single attachment or comment thread."
Jordan Cousins
Director of CX Operations at Who Gives A Crap
From Legacy Systems to Modern Workspaces — Supporting a lot of Platforms
Powering secure migrations for over 20,000 teams, including native integrations for:
Asana
Avaza
Basecamp
ClickUp
CSV
Freedcamp
GitHub
GitLab
Jira Software
Monday
Shortcut
Smartsheet
Teamwork
Trello
Wrike
Zoho Projects
Check the name for typos or leave us a message.
Don’t see your project management tool listed?
Migration Solutions
Predictable, Volume-Based Pricing
Our Pay-Per-Record model eliminates recurring subscriptions. Tiered pricing ensures cost-efficiency for high-volume enterprise migrations.
One-Time Fixed Cost
Pay only for the data migrated, ensuring total budget predictability.
Tiered Volume Discounts
Costs scale down as volume scales up, ensuring large-scale transfers remain cost-effective.
Flexible Support Tiers
Select the level of technical oversight your project requires—from self-service automated migrations to dedicated concierge engineering.
Performance Guarantee
Our pricing includes technical support and error resolution. If a record fails, our team resolves the issue without additional billing.
The Migration Wizard will scan your record count to provide a base estimate.
You can then add service packages or adjust mapping options to fit your project scope.
Custom Engineering for Complex Data Architectures
For organizations with legacy systems or non-standard logic, Project Management Migration provides custom engineering to bridge the gap between incompatible schemas and proprietary environments.
Legacy & Niche Integration
Beyond our standard integrations, our engineers can develop custom API bridges to extract data from niche or in-house platforms.
Complex Data Transformation
We execute scripted logic during the migration to handle workspace merging, hierarchy restructuring, or conditional mass-tagging.
Architectural Expertise
We specialize in migrations that require deep technical adjustments, a capability trusted by global enterprises to handle high-complexity data moves.
Technical Consultations
Access migration engineers who understand database relationships and API constraints to ensure your data architecture remains intact.
Schema Mapping & Configuration Control
Our configuration environment eliminates "black box" migrations. You define the logic; our engine handles the execution.
Granular Field Mapping
Match standard and custom fields to their exact equivalents in the target.
Relational Logic Preservation
Maintain links between assignees, task dependencies, and subtasks without manual re-linking.
Visual Configuration Workspace
Bridge disparate platform schemas through a no-code interface, replacing the need for custom mapping scripts.
Pre-Migration Validation
Execute a Free Demo to verify how your mapping logic renders with live data samples before the production transfer.
Iterative Sandbox Validation
Accuracy is the result of rigorous testing. Relokia’s Free Demo Migration is a full-scale engine simulation, allowing you to run unlimited iterations to fine-tune configuration before the production transfer.
High-Fidelity Simulation
Every demo utilizes the same API logic as a full-scale migration. The data rendering in your demo is an exact preview of the final result.
Iterative Refinement
Adjust custom fields or status mapping and re-run the demo. Refine the logic until all task hierarchies and attachments align with your target schema.
Targeted Record Testing
Select up to 20 high-complexity records to validate how the engine handles deep nesting and large attachments.
Technical Oversight & Migration Engineering
Relokia provides direct access to specialists to navigate API constraints, complex permissions, and non-standard configurations.
Specialist-Led Configuration
Technical guidance on field mapping and permissions to ensure environment readiness.
Proactive Logic Troubleshooting
Analyze sandbox data rendering to resolve logic discrepancies before production transfer.
Platform Architecture Expertise
Access specialists with deep knowledge of Jira, Asana, Monday.com, and 50+ other ecosystems for cross-platform compatibility.
Rapid Technical Resolution
Optimized for high-stakes moves, our support team is prioritized for rapid response and deep-level architectural problem-solving.

Ready for a Fresh Start? Let’s Move Together.
Eliminate technical debt and modernize your workflow. Join over 20,000 companies that have automated their transitions with 1:1 data parity.
No credit card required Zero operational downtime Unlimited Configuration Iterations







